In today’s enterprise environment, seamless and secure access across applications is critical. Organizations increasingly rely on Single Sign-On (SSO) to simplify user authentication and improve security posture. If you’re already leveraging Infor’s suite of products, you might be surprised to learn that Infor LTR (Lawson Technology Runtime)—commonly seen as middleware—can act as a powerful SSO tool, much like Infor OS.
At Nogalis, we’ve helped numerous organizations harness Infor LTR as a Security Token Service (STS), enabling robust, federated SSO integrations across Azure AD, AD FS, Okta, and other SAML 2.0-compliant identity providers. This article outlines how Infor LTR can simplify your authentication landscape while ensuring scalability and security.
What Is Infor LTR?
Infor LTR is the core runtime wrapper for Infor web applications and will be supported until at least 2029. While often viewed as an infrastructure component, it also functions as a flexible STS, enabling secure federated identity across your enterprise apps.
Why Use Infor LTR as Your STS?
- Federated SSO across multiple Identity Providers (IdPs)
Infor STS supports Azure AD, MS Entra, AD FS, Okta, and any SAML 2.0-compliant provider.
- Centralized SAML Authentication
You can configure all your applications to use Infor STS as the single point of SSO integration.
- Long-Term Viability
With support guaranteed into 2029, LTR is a stable investment in your identity infrastructure.
How It Works – The Big Picture
- Establish Trust between your application and identity provider using STS.
- Exchange Federation Metadata between STS and your IdP.
- Configure your applications to delegate authentication to Infor STS.
- SAML-based handshake manages identity, assertions, and access.
Installation & Setup
Step 1: Migrate LTR to STS Mode
Using the LTR ISO, mount and run (in a command utility):
setup.exe –v”MIGRATETOSTS=true”
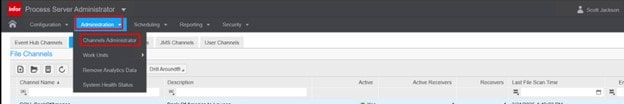
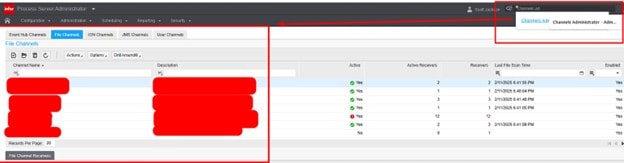
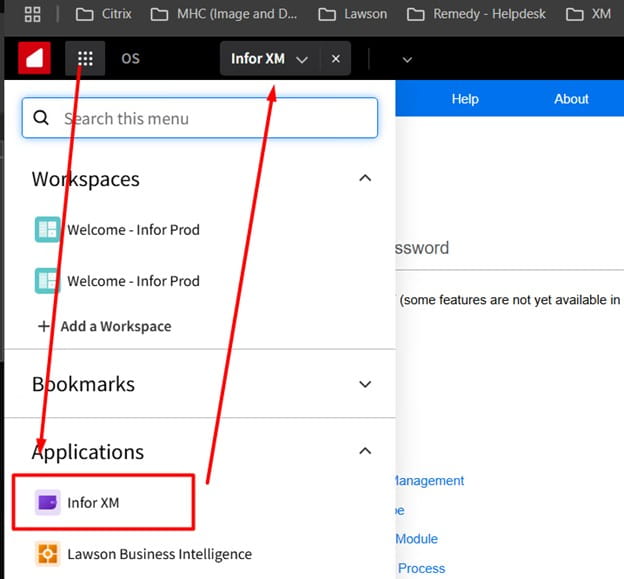
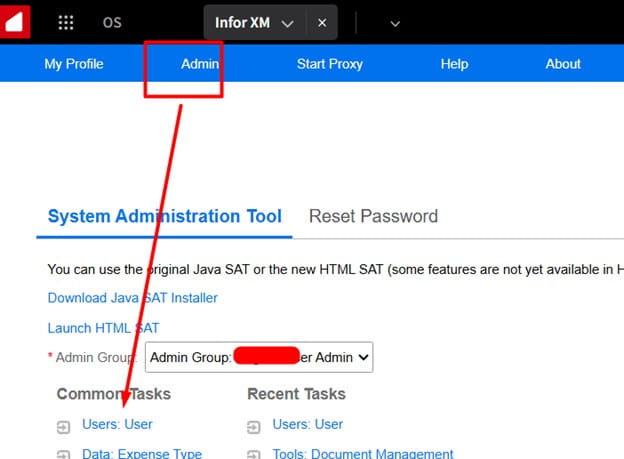
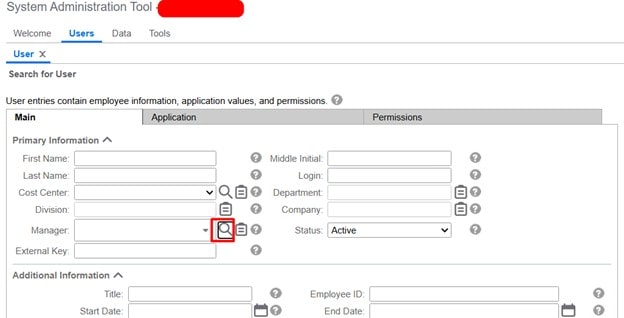
Step 2: Access STS Admin
This is your hub for managing Identity Providers (IdPs) and Service Providers (SPs). You’ll:
- Add/Edit IdP connections
- Add/Edit SP connections
- Download metadata files and certificates
Identity Provider Configuration
🔹 Azure AD
- Create a Non-Gallery App in Azure
- Upload the Infor STS SP Metadata file
- Export the Azure AD IdP Metadata and import it into STSAdmin
🔹 AD FS
- Add a new Claims-Aware Relying Party Trust
- Import the Infor STS SP Metadata XML
- Download FederationMetadata.xml from AD FS and import it into STS
🔹 Okta
- Create a SAML App Integration in Okta
- Manually configure Entity ID and endpoints (Okta doesn’t accept SP metadata files)
- Download and import Okta’s IdP Metadata XML into STS
Application Configuration
In your Infor or third-party app:
- Set SSO Service URL to:
https://your-ltr-server.com:9553/inforsts/infor/{GUID}/idp/samlSSO
- Configure SAML properties:
- UsernameField
- PasswordField
- SLOUrl
- Upload STS signing certificate as the IdP certificate in your app
- Export app’s signing cert, then import it into STS Admin
Final Checklist – What You’ve Done
✅ Downloaded IdP federation metadata
✅ Downloaded STS SAML SP metadata
✅ Uploaded metadata files to STS and your IdP
✅ Configured your app to use Infor STS as the SSO provider
✅ Completed mutual trust between your application, STS, and identity provider
Ready to Get Started?
At Nogalis, we specialize in Lawson and CloudSuite implementations, migrations, and custom development. Whether you’re looking to modernize your identity strategy or get more from your Infor investment, we’re here to help.
📧 Contact us at:
Desi Houze – desi@nogalis.com
Tan Rezaei – tan@nogalis.com
🔗 Learn more about our Lawson Data Archive Solution